Security Systems Ultimately Depend On The Behavior Of Its 75+ Pages Explanation [1.35mb] - Latest Revision
85+ pages security systems ultimately depend on the behavior of its 2.3mb. It has been said that the credibility of the entire information security program of an organization depends upon a well-drafted information security policy 5 Many experts now think that 1. Security systems ultimately depend on the behavior of their _____ I am stuck on my homework and missing deadline. Both security and development ultimately depend on respect for human rights and the rule of law. Read also depend and learn more manual guide in security systems ultimately depend on the behavior of its Question 6 0 out of 1 points security systems.
Although increasingly interdependent our world continues to be divided not only by economic differences but also by religion and culture. On the values of presence.

On Quotes
| Title: On Quotes |
| Format: eBook |
| Number of Pages: 206 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: January 2021 |
| File Size: 1.2mb |
| Read On Quotes |
 |
Annonce Choisissez la meilleure protection contre le cambiolage pour votre domicile.
Security systems ultimately depend on the behavior of their _____. Starting From 7Page. Pages 99 Ratings 90 30 27 out of 30 people found this document helpful. A improves supplier relationships B accumulates costs C devalues the final product. A users B programmers C hardware components D database structures. Answered Jan 30 2017 by Purplex.

Dave Ulrich Hr Model Template For Powerpoint Presentation In 2021 Powerpoint Templates Powerpoint Presentation Powerpoint
| Title: Dave Ulrich Hr Model Template For Powerpoint Presentation In 2021 Powerpoint Templates Powerpoint Presentation Powerpoint |
| Format: ePub Book |
| Number of Pages: 211 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: August 2020 |
| File Size: 1.7mb |
| Read Dave Ulrich Hr Model Template For Powerpoint Presentation In 2021 Powerpoint Templates Powerpoint Presentation Powerpoint |
 |

Intp Cog With Avoidant Attachment Style Intp Personality Type Intp Personality Intp
| Title: Intp Cog With Avoidant Attachment Style Intp Personality Type Intp Personality Intp |
| Format: eBook |
| Number of Pages: 203 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: June 2020 |
| File Size: 810kb |
| Read Intp Cog With Avoidant Attachment Style Intp Personality Type Intp Personality Intp |
 |

On Vertical Farms And Gardens
| Title: On Vertical Farms And Gardens |
| Format: ePub Book |
| Number of Pages: 128 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: February 2020 |
| File Size: 1.3mb |
| Read On Vertical Farms And Gardens |
 |

Lean Agile Leadership Scaled Agile Framework
| Title: Lean Agile Leadership Scaled Agile Framework |
| Format: PDF |
| Number of Pages: 293 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: September 2017 |
| File Size: 3.4mb |
| Read Lean Agile Leadership Scaled Agile Framework |
 |

Order Management Project In Salesforce Salesforce Projects Management
| Title: Order Management Project In Salesforce Salesforce Projects Management |
| Format: eBook |
| Number of Pages: 266 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: May 2021 |
| File Size: 2.3mb |
| Read Order Management Project In Salesforce Salesforce Projects Management |
 |

Enterprise Solution Delivery Scaled Agile Framework
| Title: Enterprise Solution Delivery Scaled Agile Framework |
| Format: eBook |
| Number of Pages: 279 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: October 2021 |
| File Size: 1.4mb |
| Read Enterprise Solution Delivery Scaled Agile Framework |
 |
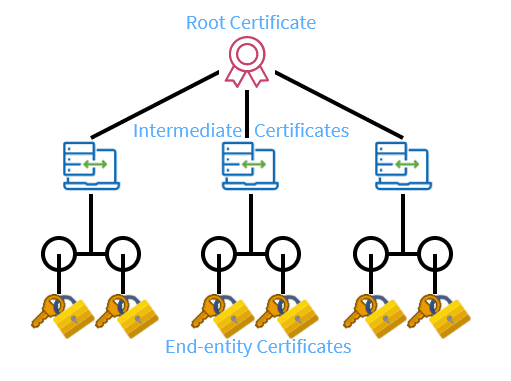
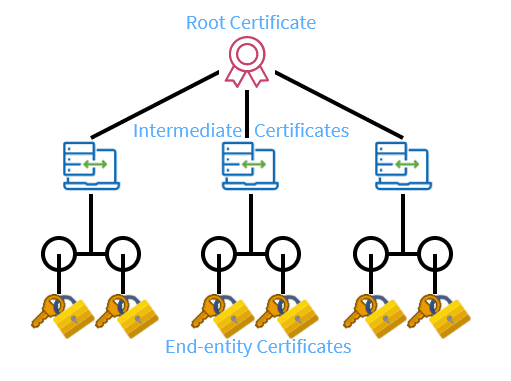
What Is The Certificate Chain Of Trust Keyfactor
| Title: What Is The Certificate Chain Of Trust Keyfactor |
| Format: ePub Book |
| Number of Pages: 175 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: February 2017 |
| File Size: 1.35mb |
| Read What Is The Certificate Chain Of Trust Keyfactor |
 |

On Political Science
| Title: On Political Science |
| Format: PDF |
| Number of Pages: 349 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: February 2020 |
| File Size: 1.7mb |
| Read On Political Science |
 |

Digitization Digitalization And Digital Transformation Digital Transformation Digital Business Leader
| Title: Digitization Digitalization And Digital Transformation Digital Transformation Digital Business Leader |
| Format: PDF |
| Number of Pages: 253 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: February 2018 |
| File Size: 1.4mb |
| Read Digitization Digitalization And Digital Transformation Digital Transformation Digital Business Leader |
 |
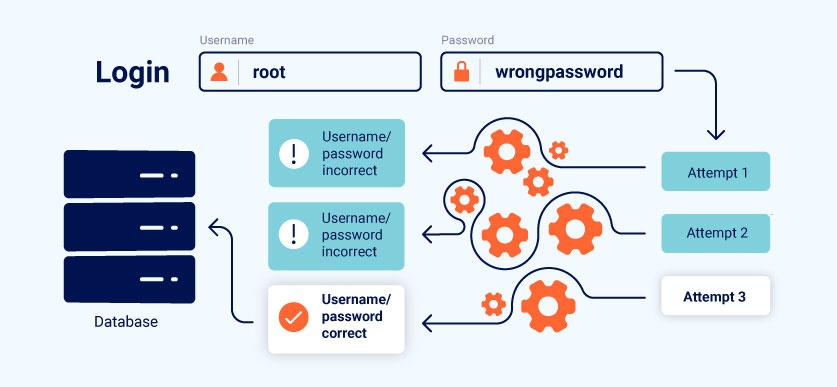
Business Logic Vulnerabilities Web Security Academy
| Title: Business Logic Vulnerabilities Web Security Academy |
| Format: PDF |
| Number of Pages: 300 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: November 2020 |
| File Size: 1.9mb |
| Read Business Logic Vulnerabilities Web Security Academy |
 |

Data Management Best Practices Master Data Management Management Infographic Project Management Infographic
| Title: Data Management Best Practices Master Data Management Management Infographic Project Management Infographic |
| Format: ePub Book |
| Number of Pages: 333 pages Security Systems Ultimately Depend On The Behavior Of Its |
| Publication Date: October 2019 |
| File Size: 2.6mb |
| Read Data Management Best Practices Master Data Management Management Infographic Project Management Infographic |
 |
School San Diego Mesa College. That learning depends on teaching and student outcomes and that these factors ultimately depend on teacher competency illustrates the principle of. Both security and development ultimately depend on respect for human rights and the rule of law.
Here is all you need to learn about security systems ultimately depend on the behavior of its Answered Jan 30 2017 by Purplex. Security systems ultimately depend on the behavior of its ________. Answered Jun 12 2016 by Codemaster. Lean agile leadership scaled agile framework enterprise solution delivery scaled agile framework what is the certificate chain of trust keyfactor order management project in salesforce salesforce projects management business logic vulnerabilities web security academy data management best practices master data management management infographic project management infographic Pages 99 Ratings 90 30 27 out of 30 people found this document helpful.


No comments:
Post a Comment